Similar Coding Tools
What is Online SHA512 Encrypt/Decrypt?
SHA512 Encrypt/Decrypt is a free online tool for generating SHA512 hashes from strings and decrypting SHA512 hashes to strings. In other words, this tool is a combination of SHA512 hash generator and SHA512 decrypter. SHA512 is a hashing function that creates a unique 512-bit hash with 128 characters long for every string. After MD5 started to lose its popularity because of its vulnerabilities, people started to look for new hashing functions as a replacement. SHA256 and SHA512 was founded for this purpose which have more strength for collusions than MD5 and have less vulnerabilities.
People are asking whether to use SHA256 or SHA512, which one is safer and what is the main difference between SHA256 and SHA512. The main difference is SHA256 generates a 64 characters long output while SHA512 generates 128. That means SHA512 is more collusion resistant. In terms of security, they are identical because both are open to dictionary attacks and brute force attacks. If you want to hash your passwords in your databases, think twice since short length strings which converted to SHA256 or SHA512 can be easily cracked/decrypted with modern computers as this tool offers. In terms of storage, people tend to use SHA256 because it takes up half space in the database.
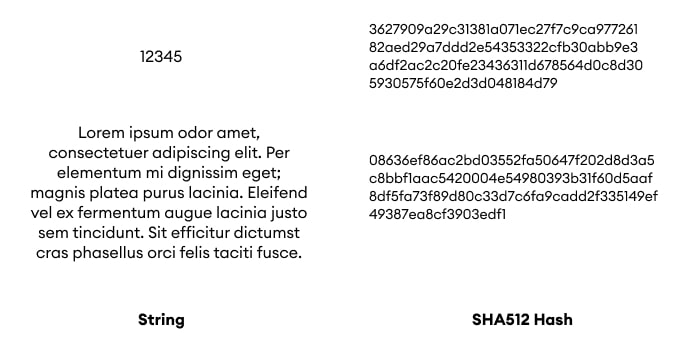
Here is a representation of how SHA512 encoder decoder works; there are two different strings with different character lengths, both produces unique SHA512 hashes with 128 characters long.
Encryption and decryption process is same for SHA256 and SHA512. It can be decrypted either by a dictionary attack or a brute force attack. This tool uses a list which includes most common 100k passwords for the first method. If this does not work, you can skip to the second method which is more time consuming.
How to use Online SHA512 Encrypt/Decrypt?
You can encode or decode your string into/from SHA512 by following the guide below.
- Generating a SHA512 has is straightforward. Just enter your text into input area and press "Encrypt" button.
- For SHA512 decryption, best practice is to use default settings first which looks for a common password dictionary. If there is no result, you can widen your trials by extending character sets which is available in "Decryption Settings".