Similar Coding Tools
What is Online SHA1 Encrypt/Decrypt?
SHA1 Encrypt/Decrypt is a free online tool for generating SHA1 hashes from strings and decrypting SHA1 hashes to strings. In other words, this tool is a combination of SHA1 hash generator and SHA1 decrypter. SHA1 (or SHA-1), also known as Secure Hash Algorithm 1, was published in 1995 by the National Security Agency (NSA) in the USA. Its former version SHA-0 was released in 1993, but it is withdrawn from the public domain and replaced with SHA1 which is claimed to be better in terms of security even there is a little change in the method.
SHA1 has a 160-bit hash output which corresponds to a 40 character string. It has been the most used hash function in the world for years. After years of usage, people found some weaknesses about SHA1 related to collusions and attacks. Around 2005, people were starting to advice not to use SHA1 because of security reasons as it is weak to well-funded attackers. In 2010's, it is advised to replace it with a more secure alternative. Even though SHA1 is not a secure hash function, it is still used in some places like data verification, creating unique identifiers, file checksums etc. For example, GIT (version control system) uses SHA1 for addressing commits.
For storing passwords or critical data or signing certificates, it is not recommended to use SHA1. Later alternatives like SHA2 or SHA3 are better for this purpose. But still it can be useful for other purposes. NIST (National Institute of Standards and Technology) recommends replacement of SHA1 with other alternatives as of 2010. SHA1 is cracked more than once officially and people found collusions, that is where 2 different strings creates the same hash value, which makes it an untrustworthy algorithm.
Since SHA1 is an irreversible function as all hash functions, there isn't an easy way like a function or method to decrypt it directly. Therefore, the easiest and most common way for decryption of SHA1 is to use trial & error method. While using this method, you can either use a dictionary attach, which can be defined as an iteration over a huge, predefined list, or you can use a brute force method which is an iteration over a small list of characters. In brute force method, it is important to select the set of characters that you want to use for brute forcing, since it may take a long time to find a match if the character list is long as the total number of all combinations will increase significantly as the list become bigger and bigger.
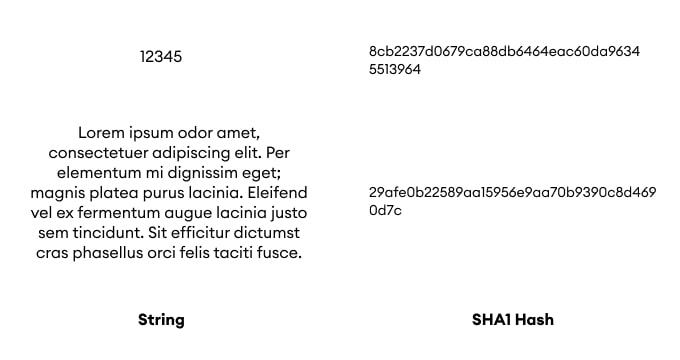
Here, you can see how SHA1 encoder decoder works; we have 2 different input which has different character length, both are represented with unique SHA1 hashes with 40 characters long. You can address, identify and distinguish long data sets with SHA1 hashes with those 40 characters long string easily.
How to use Online SHA1 Encrypt/Decrypt?
For encoding or decoding SHA1, you can follow the steps below:
- Encryption is direct. Put your input text in input field and click "Encrypt" for generating SHA1 hash.
- SHA1 decryption has a 2-step flow. It is advised to use common password list first. It is much faster if the hashed text is in the predefined list. If it does not work, you can use brute force by defining your character set from "Decryption Settings".